Overview
- Discoverer: Connor Neff
- Vendor & Product: DotNetNuke
- Version: 9.5
- CVE Number: CVE-2020-11585
Introduction
There is an information disclosure issue in DotNetNuke CMS (DNN) v.9.5 within the built in Message Center Module. A registered user is able to enumerate any file in the Admin File Manager that is not contained in a secure folder by sending themselves a message with the file attached.
Demo
To set up the demo for the attack, I uploaded a file named “password.txt” in the root DNN folder. The root folder, by default, is not a secure folder so the file will be accessible.
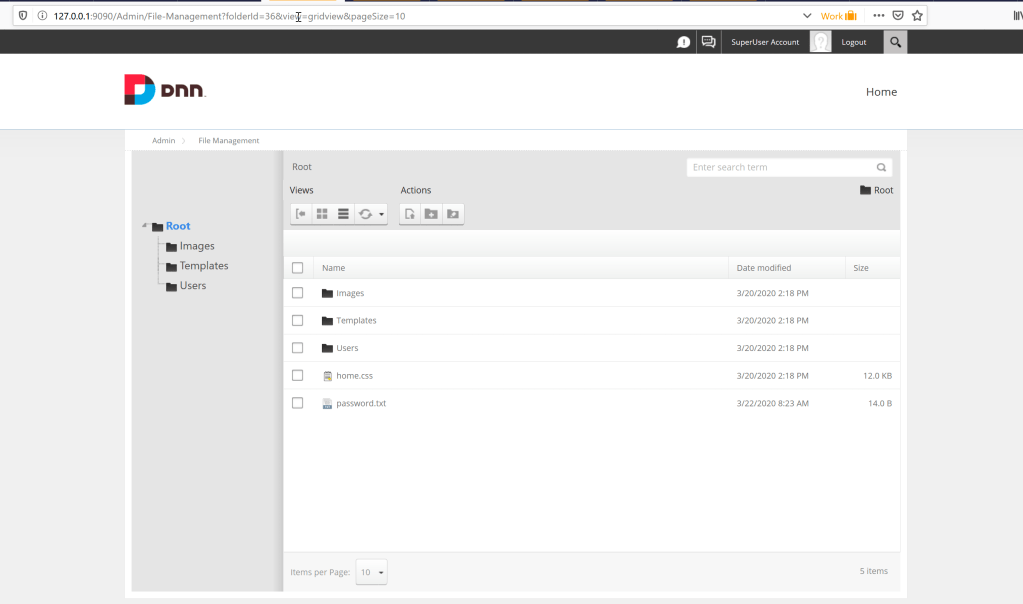
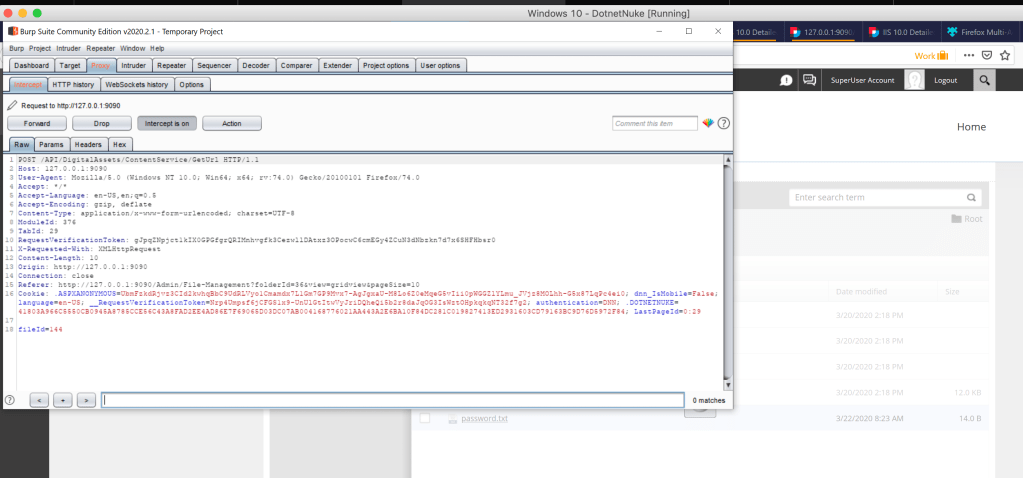
The file has a “fileId” of 144 as shown below.
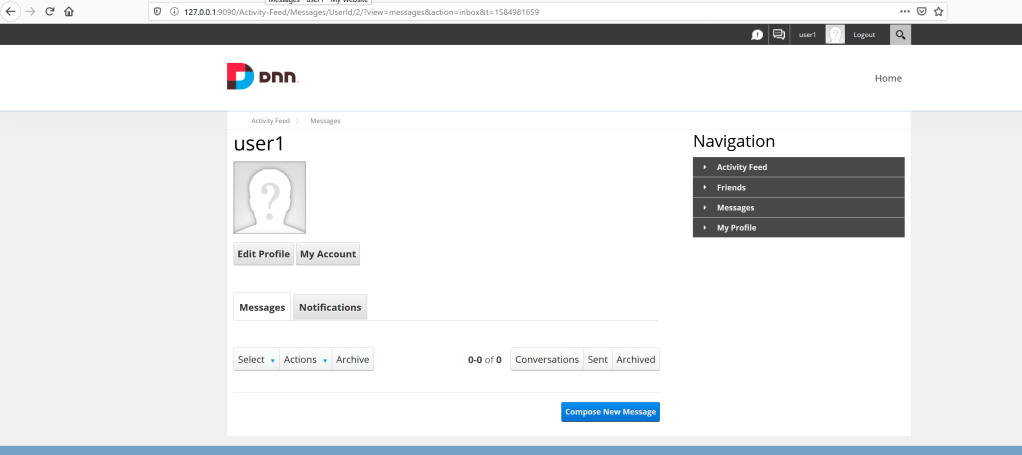
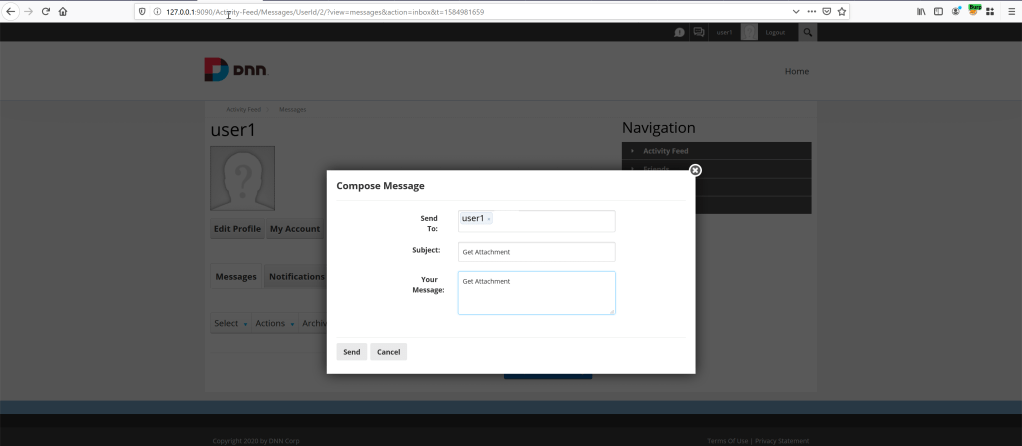
To start the attack, log into a registered users account. Go to the Messaging module at “https://yoursitehere/Activity-Feed/Messaging/Userid/<Registered User ID>”.
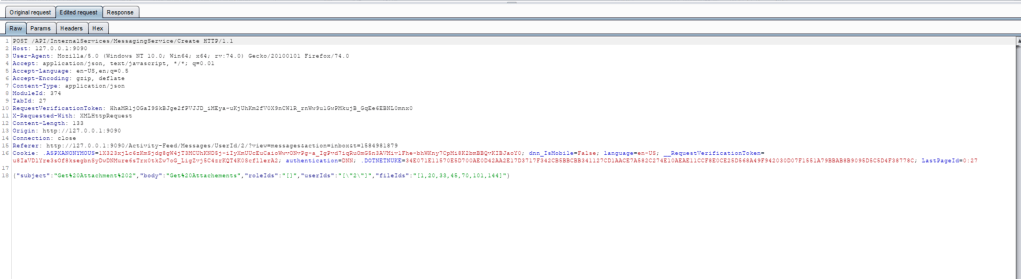
Compose a new message and set up Burp Suite to intercept the message before pressing send.
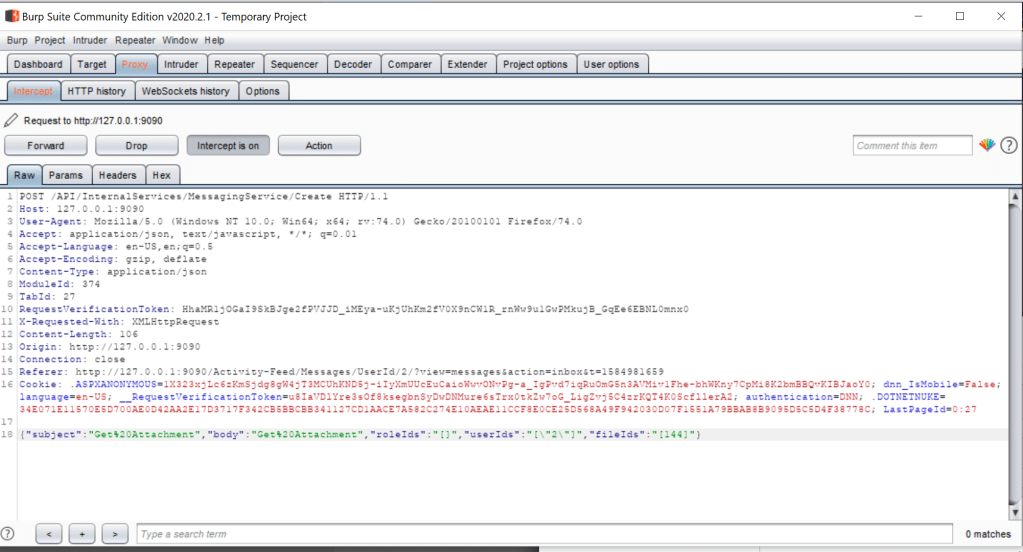
Once the message is sent, go to the Burp Suite intercepted web request and modify the parameter “fileIds” and insert the file ID.
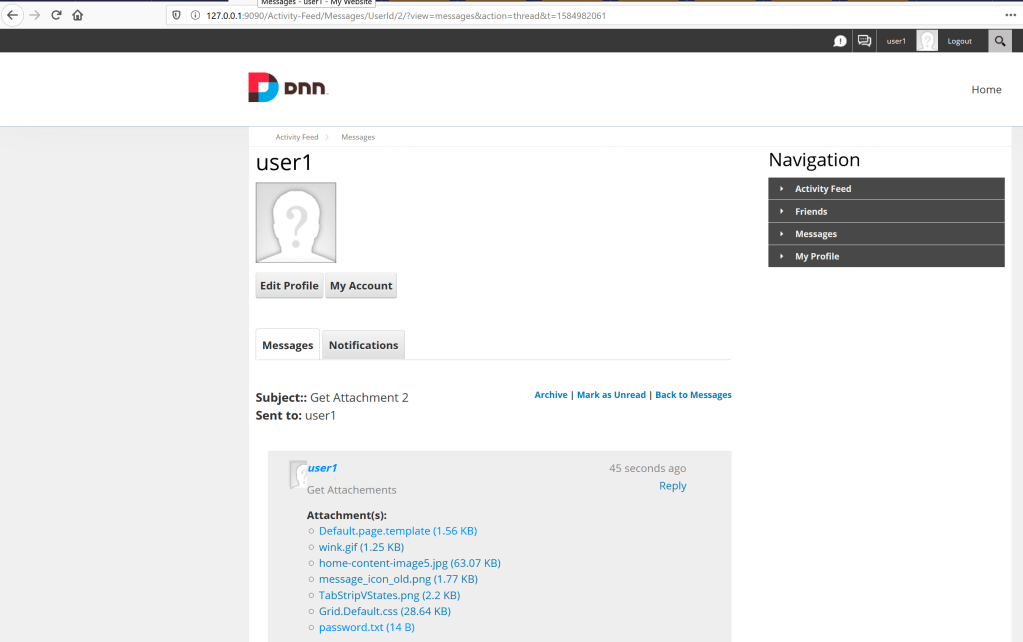
This attaches the “password.txt” file to the message and you are able to open up the file within the sent Message.
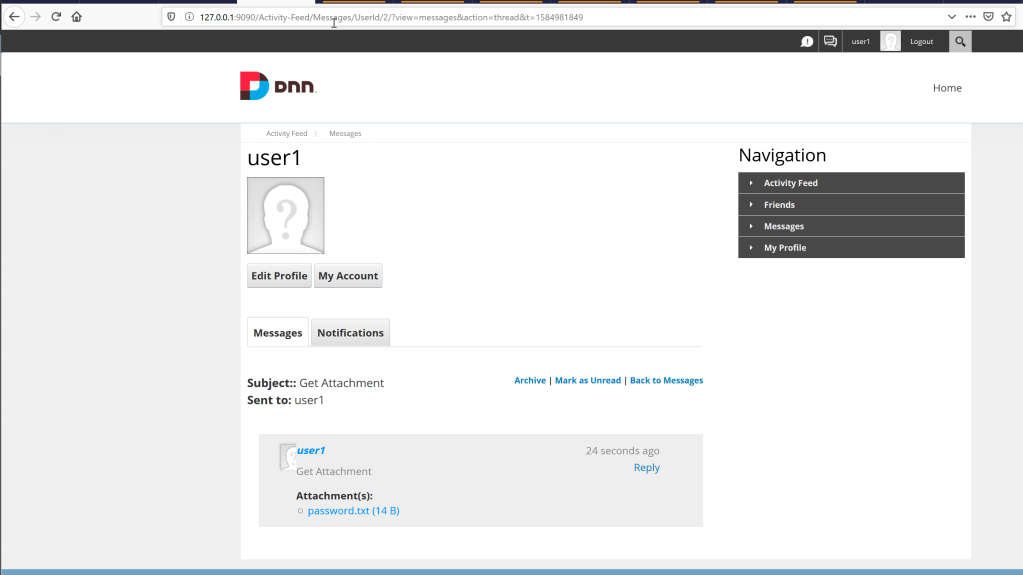
The “fileIds” parameter makes accessing these files simple due to the easily guessable number identifier. The ID iterates by one each time a new file is uploaded.
A user is also able to upload multiple file ID’s in one request which makes it easier to enumerate files in a single request.
Impact
This vulnerability could help an attacker easily discover sensitive information hosted on the DNN website without having to know the website file path to access the file.
Mitigation
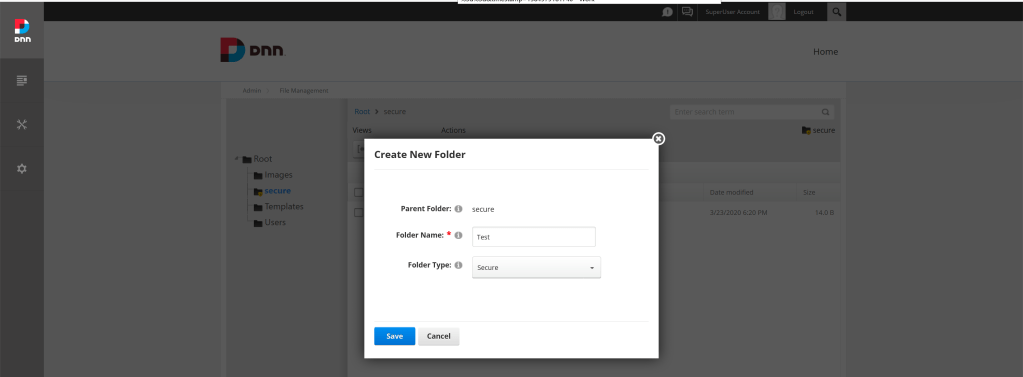
To mitigate this vulnerability, ensure all sensitive files are stored in a “secure” folder. “Secure” folders need to be created by an administrator within the File-Management module (see screenshot below). By default the root folder is not a “secure” folder. All files stored in the root directory are not considered secure.